Advanced BCS Deep Scan Platform for Smart Contract Security
With Blockchain threats becoming increasingly prevalent and malicious, passive protection methods are no longer adequate. Many regulatory bodies now demand security audits as part of their compliance requirements. Finding and isolating vulnerabilities and weak security defenses is the first step toward lowering your security risk posture.
Plenty of open source smart contract vulnerability scanners are available, but all of them have either functional limitations or complex user experience to execute the scanning. Some tools come with writing slow and chunky command lines to execute the scan the developers have to write and run in the tool for detecting vulnerabilities. This is a very time-consuming and exhaustive task hence smart contract developers generally do not run many VM tools for checking code weaknesses during the developmental stage. This leaves the door open for vulnerabilities in later stages and can result in the theft of millions of dollars by cyber hackers.
As the trusted blockchain security firm, BlockChainSentry has tailored its smart contract security platform to suit large established businesses, smart contract developers, security auditors, and CISOs. The user-friendly BCS smart contract security platform does not require you to write any code lines for reviewing smart contracts. Most scanners stop at detecting 40 of the known vulnerabilities. This leaves the door open for other known vulnerabilities. Our BCS scanners are built for deep scans. We offer 116+ detectors and we detect vulnerabilities that are “invisible” to other scanners. Potentially millions of dollars are saved.
Why do your Blockchain Projects need a security analysis?
Due to the Blockchain ecosystem's rapid expansion, many investments have been incurred into smart contracts that are often unaudited. Security of smart contracts is never optional or by choice, it is inevitable to include vulnerability management measures by using smart scanning tools that can automatically identify code vulnerabilities and give remediations in real-time. Sighting the recent cyber attacks on various blockchain projects, the security analysis is becoming crucial. In the first half of 2022, there were 187 security incidents, with damages reaching $1.976 billion as of June 30. In the first half of the year, May and June were the months with the most safety concerns. A loss of about $1.84 billion, or 77% of these security incidents, which accounted for 93% of the total loss from security incidents, were caused by attackers using the project's vulnerabilities. A loss of almost $130 million was driven by scams, including phishing and rug pull attacks, in about 21%. As more and more DeFi platforms are created, they must undergo careful vulnerability management processes and auditing before deployment on the blockchain node.
How BlockChainSentry's Security Analysis platform can help you?
We use our in-depth knowledge of blockchain technology and programming languages to detect and remediate vulnerabilities. We ensure that every step of the vulnerability management process will go smoothly with the diverse skill sets of our developers and web3-based applications
BlockChainSentry's Vulnerability Management Platform
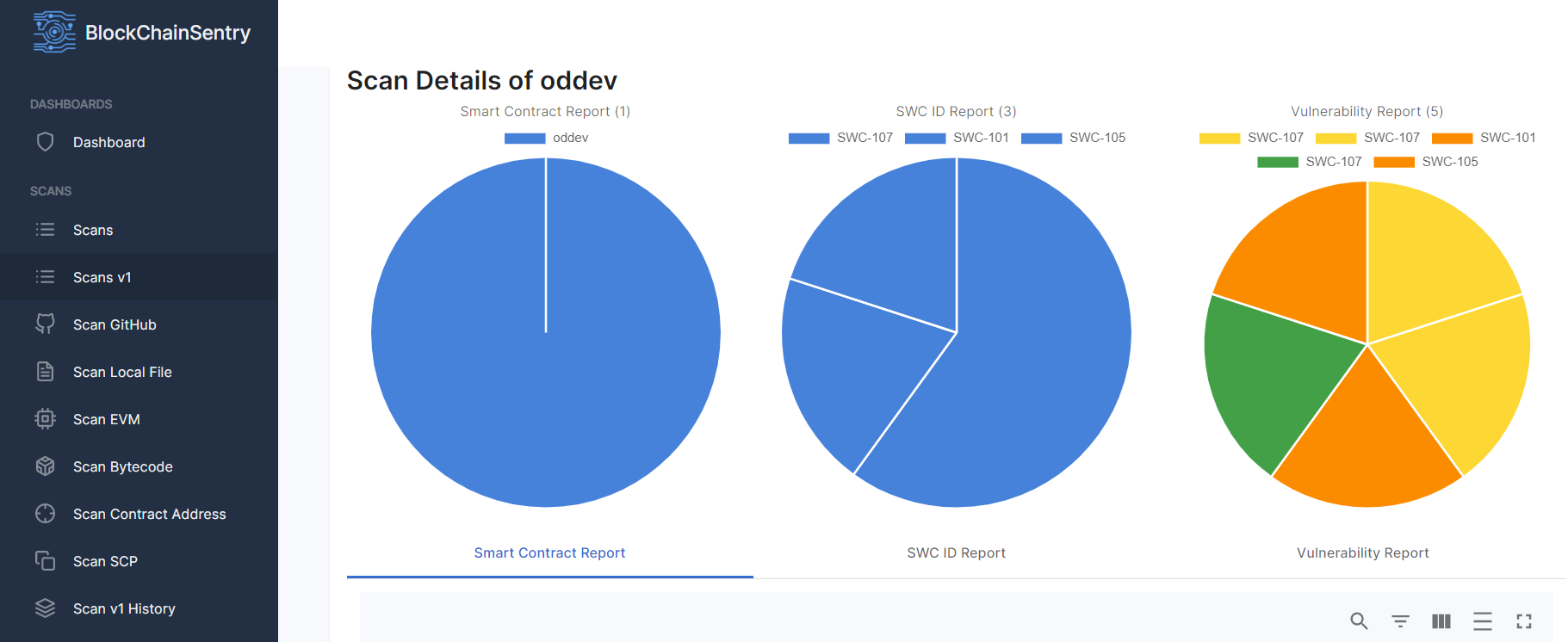
The Vulnerability Management System (VMS) application from BlockChainSentry offers the fastest, most precise, always-on, and continuous solution in the market to assist you in implementing comprehensive vulnerability management in your business.
We assist you in automating all phases of vulnerability management, including vulnerability scanning, identification, evaluation, prioritization, and remediation. Our application is Web3-based and uses a comprehensive model to function at an unmatched speed and precision. To make your scanning efforts simple, you can scan your code through
- A local IDE plugin
- GitHub
- Bytecode
- Smart contract address
We also recognize the significance of applying the correct standards. We can do vulnerability assessments for fungible, non-fungible, and multiple tokens because we deal with the ERC20, ERC721, and ERC1155 standards.
Developers can scan every EVM-based blockchain project with our VMS application, including Ethereum, Solana, Polygon, and Quorum, which includes public and private blockchain networks and any hybrid model. Our application carefully examines the code for vulnerabilities that might prevent transactions from being carried out securely. Our stand-alone application assists developers in producing high-quality smart contracts by strengthening the code and enhancing its security
BlockChainSentry Vulnerability management solution provides cyber-hygiene by automating and coordinating safeguards to protect your Defi, Crypto exchanges, NFTs, gaming, supply chain, healthcare, and enterprise blockchain applications from online threats.
Security Audits
We handle smart contract audits with deep precision, before making the finished product available, we carefully review every line of code. As a blockchain audit company, we use industry-standard techniques, methods, and algorithms to address even the most minor problems. So, before the smart contract is implemented on the blockchain, we ensure it is resistant to any vulnerabilities.
Our Audit structure includes,
- Deep scan against the known vulnerabilities
- Gas usage analysis
- Code review
- Providing a detailed report of detected issues
- Verification of fixes
- Final audit report preparation & publishing
Transparency is important to us, particularly when it comes to smart contract audits. Once our team has identified every error—whether functional, optimization security-related or general—we provide a report that details each stage of the process. We provide information on the defects' severity, our suggestions, illustrations of errors, and a thorough audit description. With the help of our audit report, you'll know precisely what has to be addressed and how.
Why Choose BlockChainSentry?
Our diligent security audit experts review the code to identify security issues with the smart contract. We enhance the contract's functionality and general security by resolving those issues. Our team offers the best defenses against numerous vulnerabilities for your smart contracts. To avoid severe losses and project failure, we address root causes early on and even after deployment with version control.
- Saves more than 50% in Audit costs
- Detects 116+ Vulnerabilities
- Reduces human errors in the Audits
- In-depth Security Audit report
- 360 Degree Visibility
- Compliance with GCPR and ERC standards
BlockChainSentry's end-to-end security solutions can support you in delivering trusted and secure smart contracts on schedule, whether you are a developer, security specialist, compliance manager, or security operations professional. Apart from Security Audits and Vulnerability Management systems, we also provide
- Threat intelligence
- Penetration testing
- DApp development
- Test Automation
- Cyber Security Services
If you have a specific idea, contact us or schedule a call because we are always open to customs security solutions. Reach out to us at hello@blockchainsentry.com