BlockChainSentry Vulnerability Management App Designed For Gas Optimization

Summary: BlockChainSentry's Vulnerability Management App is designed for gas optimization. It scans the smart contracts to detect and identify gas-focused vulnerabilities with precision and provides a remediation strategy to patch them.
What Is Gas Optimisation?
Smart contract transactions are expensive to execute as it costs ‘Gas’. To make smart contract deployment and execution cost-effective, knowing tips and tricks to optimize gas consumption is in high demand. Ethereum is an open-source, permissionless, public, blockchain-based technology initially created to enable digital currency. The decentralized Ethereum blockchain network was built in 2015 by Vitalik Buterin and Joe Lubin as an evolution of the Bitcoin protocol to provide a platform for more complex applications. Today, the Ethereum blockchain network is live and actively used in multiple industries, with thousands of use cases. It is the most widely used decentralized technology across all industry verticals, with companies such as Uber, Amazon, and Microsoft testing its use case to streamline their business processes.
Every operation in Ethereum, be it a transaction or smart contract execution, requires some amount of gas fees that need to be paid. The gas fee (GWEI) is paid in Ether. DAO developers working on different DLTs are looking for options to optimize the gas fees and improve the performance of the blockchain application.
What Is Ethereum Gas?
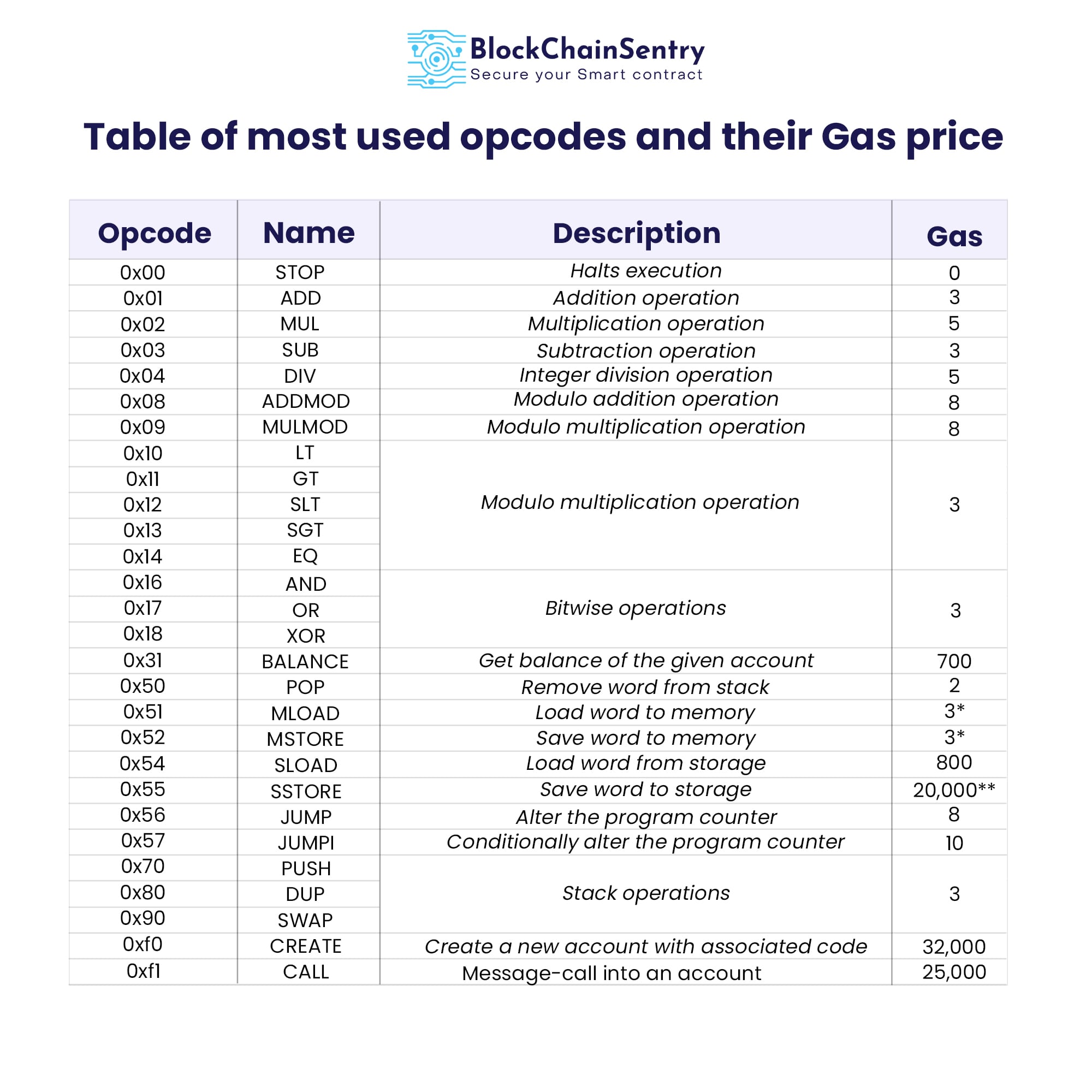
The gas is the fuel/fees the Ethereum protocol uses to execute transactions on the blockchain. As the Ethereum transaction rate increases, the gas amount has to rise to keep the Ethereum network operating efficiently. Most of the smart contracts running in the EVM are coded using Solidity. Every line of code in Solidity requires a certain amount of gas to be executed.
Transaction, Gas Price, And Gas Limit
In a blockchain system, transactions are data structures that encode the transfer of value between participants. Every transaction needs to go through a process of mining which is a method of authentication.
Transaction Fee = Gas Price * Gas Limit
Gas Price: The amount of ETH paid to miners for processing transactions on the network is referred to as the "gas price." The value of one gwei is 0.000000001 or 10-9 ETH.
Gas Limit: The gas amount in a transaction is predetermined, the total amount of gas you agree to pay for your transaction is the "gas limit."The standard gas limit for an ETH transfer is 21000 gas, but this value may vary based on the amount of processing power needed to include your transaction in the block. There must be enough gas to pay for the transaction's cost so that you don't run an "Out of gas" exception if the gas value turns out to be less than the required amount.
Factors affecting the cost of Gas Fee
- Current Gas demand
- Processing power or resources needed to process smart contracts
- Number of transactions
- Smart contract's size and required execution time
 Source: Research Paper University of Camerino
Source: Research Paper University of Camerino
Why Do We Have A Gas Fee?
Ethereum follows this Gas structure to provide the process of incentivization and to motivate miners. Ethereum relies on the mining pool's hash power, and the hash rate increases with the number of miners. Developers must make Ethereum mining as lucrative and appealing as possible to draw miners' attention to the system.
Gas Focused Vulnerabilities
Gas-focused vulnerabilities allow an attacker to launch a persistent denial-of-service attack on the contract, causing it to stop functioning properly. Since out-of-gas behavior may not frequently occur in non-attack settings, understanding these vulnerabilities requires some thought, and they are among the hardest for programmers to defend against. Some of the gas focussed vulnerabilities are
Unbounded mass operations
Unbounded mass operations are the most prevalent type of gas-focused vulnerability. The block gas limit could be exceeded in this loop operation by the user input iterating too frequently. The contract may not have been able to continue functioning as intended in these circumstances since the code may not have foreseen this scenario. All transactions attempting to iterate the loop will typically experience a denial of service since the cost of the loop's instructions exceeds the Ethereum block gas limit.
Nonisolated calls
Invoking external functionality that might result in its out-of-gas exception is another method for a contract to go out of gas. This exception may arise while calling a function.
Number of transactions
A programming error commonly expressed as a gas-focused vulnerability results from possible integer overflows. An attacker can exploit this vulnerability by adding fake functions until the overflow is triggered.
These Gas optimization vulnerabilities are very difficult to detect and manage, BlockChainSentry VMS application has Gas optimization detectors that can identify vulnerabilities and help you remediate them. If you want to know more then Contact us.